Let’s look at an old Roman age encryption scheme. Let’s say we intercepted a message from a
known Celtic hacker group. We know from experience that this group uses the characters from A to Z, then
a space, and then the numerals from 0 to 9 and employs a wrap around (moving left from A gives us 9).
The first leading pairs of letters tell us what the substitution code is using the code phrase “Trudy Jones”.
For example if the first two pairs are uy du the code is 24 and 32. This would mean that we move the first 2
Essay Writing Service Features
Our Experience
No matter how complex your assignment is, we can find the right professional for your specific task. Writing Errands is an essay writing company that hires only the smartest minds to help you with your projects. Our expertise allows us to provide students with high-quality academic writing, editing & proofreading services.
Free Features
Free revision policy
$10Free bibliography & reference
$8Free title page
$8Free formatting
$8How Our Essay Writing Service Works
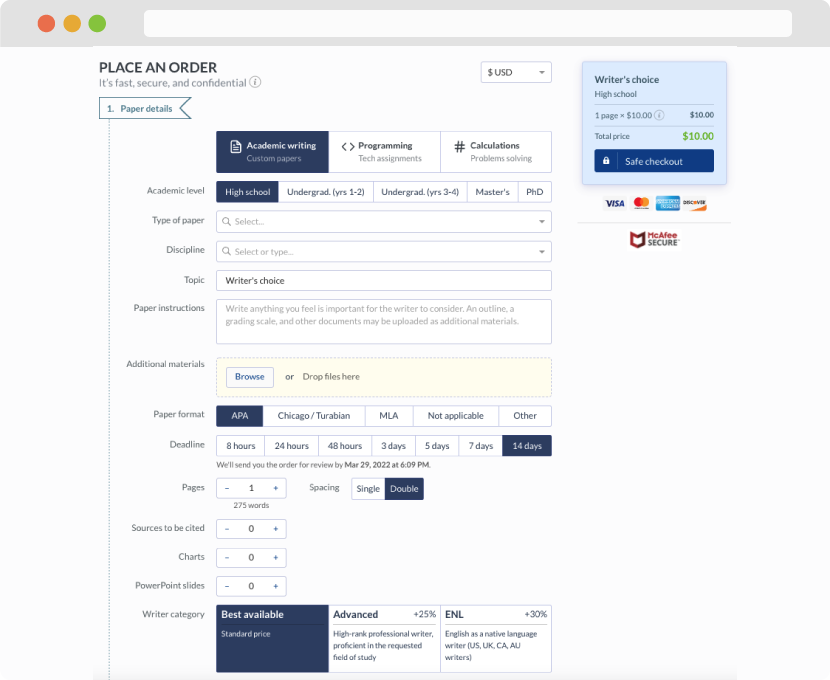
First, you will need to complete an order form. It's not difficult but, in case there is anything you find not to be clear, you may always call us so that we can guide you through it. On the order form, you will need to include some basic information concerning your order: subject, topic, number of pages, etc. We also encourage our clients to upload any relevant information or sources that will help.
Complete the order form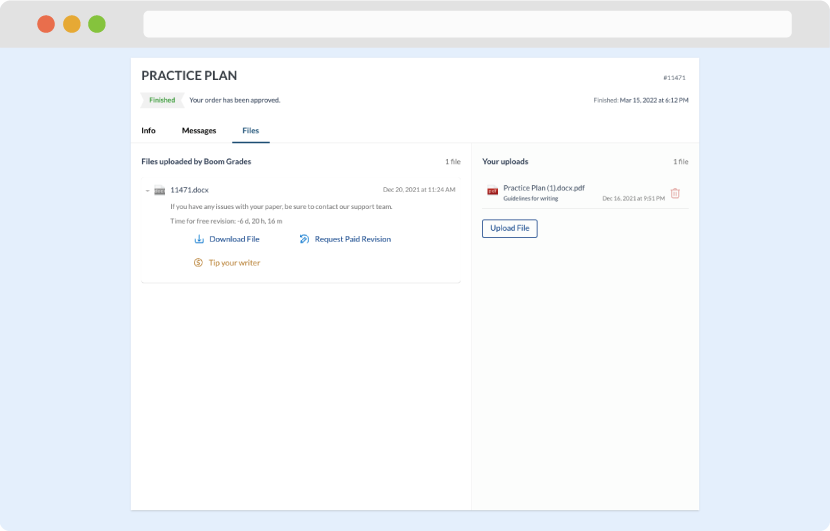
Once we have all the information and instructions that we need, we select the most suitable writer for your assignment. While everything seems to be clear, the writer, who has complete knowledge of the subject, may need clarification from you. It is at that point that you would receive a call or email from us.
Writer’s assignment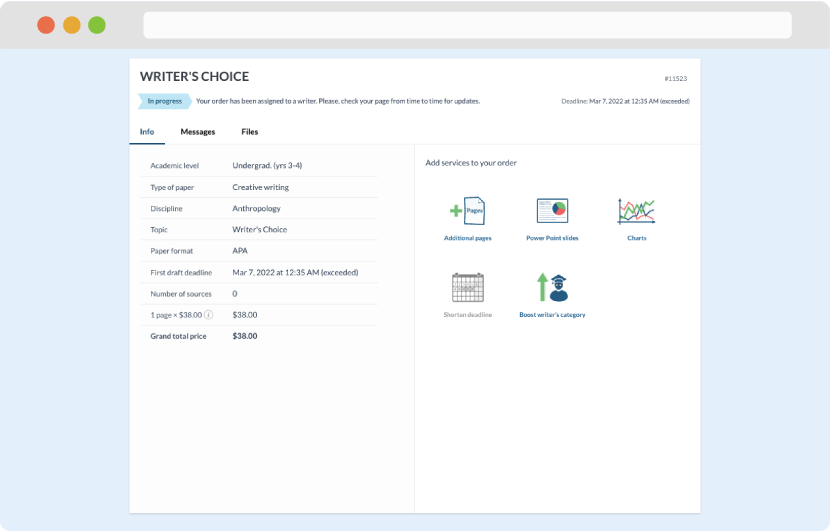
As soon as the writer has finished, it will be delivered both to the website and to your email address so that you will not miss it. If your deadline is close at hand, we will place a call to you to make sure that you receive the paper on time.
Completing the order and download